Questa guida fornisce istruzioni agli amministratori su come disabilitare l’autenticazione a due fattori (2FA) tramite la console.
Livello utente richiesto: Amministratore di sistema
Accesso alla console richiesto
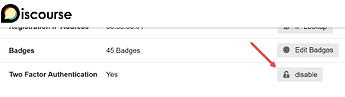
Questa guida dovrebbe essere utilizzata solo quando la 2FA non può essere disabilitata dalla pagina di amministrazione utente.
Discourse supporta tre tipi di opzioni a due fattori: TOTP (codici a 6 cifre che ruotano ogni 30 secondi), chiave di sicurezza (Yubikey, biometrica, ecc.) e codici di backup. A volte gli utenti configurano in modo errato il proprio dispositivo a due fattori, perdono o reimpostano il telefono, o in altro modo non sono più in grado di utilizzare/ottenere il fattore di due. Gli amministratori possono quindi assistere nella reimpostazione per loro conto.
Gli amministratori dovrebbero essere certi di verificare che sia l’utente a effettuare la richiesta. La disabilitazione del 2FA rende un account più facile da hackerare, quindi assicurati che non sia una parte malintenzionata a richiedere la reimpostazione.
Disabilitazione della 2FA per un utente
-
Innanzitutto, dovrai sapere quale utente sta riscontrando il problema. Ottieni il nome utente per l’utente:
-
Accedi all’applicazione rails sul tuo server tramite ssh.
Dal tuo computer locale:ssh root@=SERVER_IP=Vai alla directory dell’applicazione:
cd /var/www/discourse sudo ./launcher enter app -
Usa il rake task fornito per disabilitare tutti i metodi 2FA per l’utente:
bundle exec rake users:disable_2fa[=USERNAME=]Questo rimuoverà tutti gli autenticatori TOTP, le chiavi di sicurezza utilizzate per la 2FA e i codici di backup. Nota che le passkey non sono interessate da questo comando.