| ملخص | يسمح Discourse OpenID Connect باستخدام مزود OpenID Connect كمزود مصادقة لـ Discourse. | |
| دليل التثبيت | هذه الإضافة مدمجة مع نواة Discourse. لا حاجة لتثبيت الإضافة بشكل منفصل. |
الميزات
تهدف هذه الإضافة إلى تقديم تنفيذ بسيط لـ المواصفة. على وجه التحديد، تدعم «تدفق رمز التفويض». للبدء، اتبع تعليمات تثبيت الإضافة، أو اتصل بمزود الاستضافة الخاص بك.
يمكن استخدام إضافة oauth2-basic للاتصال ببعض مزودي OpenID Connect (حيث إن OpenID Connect مبني على OAuth2). ومع ذلك، فإن هذه الإضافة تتطلب إعدادًا يدويًا أقل بكثير، ويمكنها استخدام «رمز الهوية» JWT إذا لم يكن واجهة برمجة التطبيقات JSON متاحة.
يتم إجراء الإعداد تلقائيًا باستخدام مستند اكتشاف OpenID Connect. وفقًا للمواصفة، يجب أن يكون هذا المستند موجودًا في <nطاق المصدر>/.well-known/openid-configuration، لكن Discourse يدعم أي مسار للسماح بتنفيذات غير متوافقة (مثل Azure B2C). يتم تخزين مستند الاكتشاف مؤقتًا لمدة 10 دقائق لتحسين الأداء في المواقع ذات الزيارات العالية.
إذا تضمن مستند الاكتشاف معلمة userinfo_endpoint، فستستخدم الإضافة هذه المعلمة لجمع بيانات المستخدم الوصفية. وإلا، ستستخرج الإضافة البيانات الوصفية من id_token (وهو JWT) المقدم من طرف الرمز. الإضافة لا تتحقق من صحة توقيع JWT، لأن ذلك سيزيد التعقيد بشكل كبير. يدعم هذا القرار المواصفة:
إذا تم استلام رمز الهوية عبر اتصال مباشر بين العميل وطرف الرمز (وهو الحال في هذا التدفق)، فيمكن استخدام التحقق من خادم TLS للتحقق من المصدر بدلاً من التحقق من توقيع الرمز.
لمزودي الهوية الذين يدعمون التفويض بدون سر باستخدام «تدفق رمز التفويض مع مفتاح الإثبات لتبادل الرمز»، يجب تمكين PKCE، ويمكن إغفال إعداد client_secret.
الإعداد
خيارات الإعداد الأساسية
-
openid_connect_enabled:تمكين مصادقة OpenID Connect -
openid_connect_discovery_document: عنوان URL لمستند اكتشاف OpenID Connect. عادةً ما يكون موجودًا فيhttps://your.domain/.well-known/openid-configuration -
openid_connect_client_id: معرف عميل OpenID Connect -
openid_connect_client_secret: سر عميل OpenID Connect -
openid connect rp initiated logout: إعادة توجيه المستخدم إلىend_session_endpointبعد تسجيل الخروج. يجب أن يدعمه مزود الهوية الخاص بك وأن يكون مدرجًا في مستند الاكتشاف. -
openid connect rp initiated logout redirect: (اختياري) عنوانpost_logout_redirect_uriالذي سيتم تمريره إلى طرف تسجيل الخروج. إذا تم توفيره، فيجب تسجيله لدى مزود الهوية. -
openid_connect_authorize_scope: النطاقات المرسلة إلى طرف التفويض. يجب أن تتضمن «openid» -
openid_connect_use_pkce: تمكين مفتاح الإثبات لتبادل الرمز (PKCE) لمصادقة OpenID Connect. -
openid_connect_verbose_logging: تسجيل معلومات تفصيلية حول مصادقة openid-connect في/logs. يُنصح بإبقاء هذا الخيار معطلًا أثناء الاستخدام العادي.
خيارات الإعداد المتقدمة
-
openid_connect_token_scope: النطاقات المرسلة عند طلب طرف الرمز. المواصفة الرسمية لا تتطلب ذلك. -
openid_connect_error_redirects: إذا احتوىerror_reasonفي رد الاستدعاء على المعامل الأول، سيتم إعادة توجيه المستخدم إلى عنوان URL في المعامل الثاني. يُستخدم للتنفيذات غير العادية التي ترسل أخطاء استجابةً لإدخال المستخدم (مثل Azure B2C) -
openid_connect_allow_association_change: السماح للمستخدمين بفصل وإعادة ربط حسابات Discourse الخاصة بهم مع مزود OpenID Connect
-
openid_connect_groups_claim: اسم المطالبة في استجابة OIDC[1] التي تحتوي على مجموعات المستخدم كمصفوفة من السلاسل النصية. اتركها فارغة لتعطيل مزامنة المجموعات. انظر مزامنة المجموعات أدناه. -
openid_connect_user_field_mappings: تعيينات لمطالبات OIDC[2] سيتم تخزينها في حقول المستخدم في Discourse. يتم تحديد حقول المستخدم بمعرفها الرقمي، والذي يمكن العثور عليه في عنوان URL عند تحريرها عبر لوحة الإدارة.
مزامنة المجموعات
يمكن للإضافة مزامنة عضويات المجموعات تلقائيًا من مزود OpenID Connect الخاص بك إلى مجموعات Discourse. في كل تسجيل دخول، ستقرأ الإضافة المطالبة المهيأة من رمز OIDC وتحدّث عضويات مجموعات المستخدم وفقًا لذلك. لتمكين مزامنة المجموعات:
-
قم بإعداد مزود الهوية الخاص بك لإرجاع مصفوفة من المجموعات في إحدى المطالبات. يجب أن تكون هذه مصفوفة من السلاسل النصية.
-
اضبط
openid_connect_groups_claimعلى اسم المطالبة في رمز OIDC التي تحتوي على مجموعات المستخدم (مثلcognito:groups). بمجرد تعيينها، سيبدأ ذلك في مزامنة المعلومات مع نظام «المجموعات المرتبطة» في Discourse. -
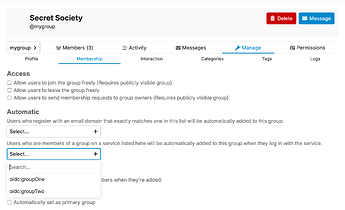
ابحث عن مجموعة Discourse التي ترغب في ربطها. انتقل إلى «الإعدادات» → «العضوية» → «تلقائي»، ثم اختر المجموعات المرتبطة للربط. يتم تعبئة قائمة القائمة المنسدلة هذه بمعلومات من مزود الهوية، لذا يجب أن يكون عضو واحد على الأقل قد سجّل الدخول لظهور خيار.
مثال على الإعداد
سنقوم هنا بإعداد إضافة openid-connect للاتصال بمزود OpenID Connect من Google. هذا يحاكي وظيفة موجودة بالفعل في نواة Discourse، لكنه يعمل كمثال سهل الوصول.
-
انتقل إلى OpenID Connect | Sign in with Google | Google for Developers واتبع التعليمات للحصول على بيانات اعتماد OAuth.
-
في نفس الصفحة، اتبع التعليمات لإضافة عنوان URL لإعادة التوجيه. يجب أن يكون
https://<منتدى_كـم>/auth/oidc/callback(بدون شرطة مائلة في النهاية) -
انتقل إلى إعدادات موقع Discourse وابحث عن “openid_connect”
-
openid connect enabled: [x] -
openid connect discovery document:https://accounts.google.com/.well-known/openid-configuration -
openid connect client id:<client-id> -
openid connect client secret:<client-secret> -
openid connect authorize scope:
openid email(مع مسافة بينهما)
-
-
لقد انتهيت. الآن سيتم تسجيل الدخول باستخدام زر «تسجيل الدخول باستخدام OpenID Connect» عبر Google
 . يمكن تطبيق نفس الخطوات هذه على مزودين آخرين مع تغييرات طفيفة جدًا.
. يمكن تطبيق نفس الخطوات هذه على مزودين آخرين مع تغييرات طفيفة جدًا.
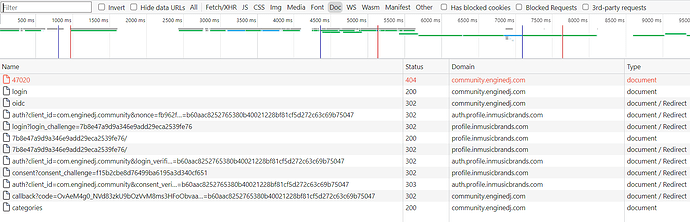
استكشاف الأخطاء وإصلاحها
بالإضافة إلى إعداد verbose_logging الموصوف أعلاه، يمكنك الوصول إلى بيانات حول ارتباطات OIDC باستخدام إضافة data-explorer:
SELECT user_id, provider_name, provider_uid
FROM user_associated_accounts
WHERE provider_name = 'oidc'
أو في وحدة تحكم rails:
User.find_by_username("david").user_associated_accounts.where(provider_name: 'oidc')
ملاحظات خاصة بالمزودين
لا تتردد في تحديث هذا إذا وجدت أي غرائب خاصة بمزود معين تتعلق بهذا التكامل:
Entra ID (سابقًا Azure AD)
أضف نطاق email، وتأكد من استخدام مستند إعداد الإصدار 2. على سبيل المثال
https://login.microsoftonline.com/{tenant}/v2.0/.well-known/openid-configuration
Azure B2C
يمكن العثور على تفاصيل عنوان URL لمستند الاكتشاف هنا: Web sign in with OpenID Connect - Azure AD B2C | Microsoft Learn
لجعل البريد الإلكتروني يعمل:
Yahoo
-
انتقل إلى https://developer.yahoo.com/apps وأنشئ تطبيقًا جديدًا
-
أدخل اسم التطبيق، واضبط نطاق الاستدعاء على نطاق المنتدى الخاص بك (مثل
meta.discourse.org) -
تحت أذونات واجهة برمجة التطبيقات، اختر الملفات الشخصية: قراءة/كتابة عامة وخاصة. هذه هي الطريقة الوحيدة التي أعرفها للحصول على عنوان البريد الإلكتروني للمستخدم
-
احفظ التطبيق
-
في إعدادات OIDC في Discourse، اضبط مستند الاكتشاف على
https://login.yahoo.com/.well-known/openid-configuration -
أدخل معرف العميل والسر من Yahoo
-
قم بتمكين إضافة OIDC
AWS Cognito
- انتقل إلى Cognito وحدد أو أنشئ مجمع مستخدمين جديد.
- عرّف تطبيقًا في عملاء التطبيق.
- اترك كل شيء على الوضع الافتراضي، لكن غيّر إعداد تدفقات المصادقة لاختيار ALLOW_REFRESH_TOKEN_AUTH فقط.
- انتقل إلى إعدادات عميل التطبيق وحدد التطبيق الجديد.
- غيّر عنوان URL للاستدعاء إلى https://yoursite.example.com/auth/oidc/callback.
- ضع علامة فقط على تدفق منح رمز التفويض ضمن «تدفقات OAuth المسموح بها».
- ضع علامة على جميع النطاقات المطلوبة (لقد وضعت علامة على جميعها).
Okta
-
قم بإعداد Discourse مع معرف عميل تطبيق Okta والسر الخاص به
-
اضبط عنوان URL لمستند الاكتشاف على
https://{your-app}.okta.com/.well-known/openid-configuration -
في Discourse، اضبط
openid connect authorize scopeعلىopenid email
مستضافون لدينا؟ هذه الإضافة متاحة في خططنا للأعمال والشركات. OAuth 2.0 & OpenID Connect Support | Discourse - Civilized Discussion
هل تحتاج إلى أتمتة تسجيلات دخول المستخدمين؟ انظر Auto-provisioning user accounts when SSO is enabled